CVE-2024-27288 – github.com/1panel-dev/1panel
Package
Manager: go
Name: github.com/1panel-dev/1panel
Vulnerable Version: >=0 <1.10.1-lts
Severity
Level: Medium
CVSS v3.1: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:L
CVSS v4.0: CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:P/VC:L/VI:L/VA:L/SC:N/SI:N/SA:N
EPSS: 0.00453 pctl0.62884
Details
1Panel open source panel project has an unauthorized vulnerability. ### Impact The steps are as follows: 1. Access https://IP:PORT/ in the browser, which prompts the user to access with a secure entry point.  2. Use Burp to intercept: 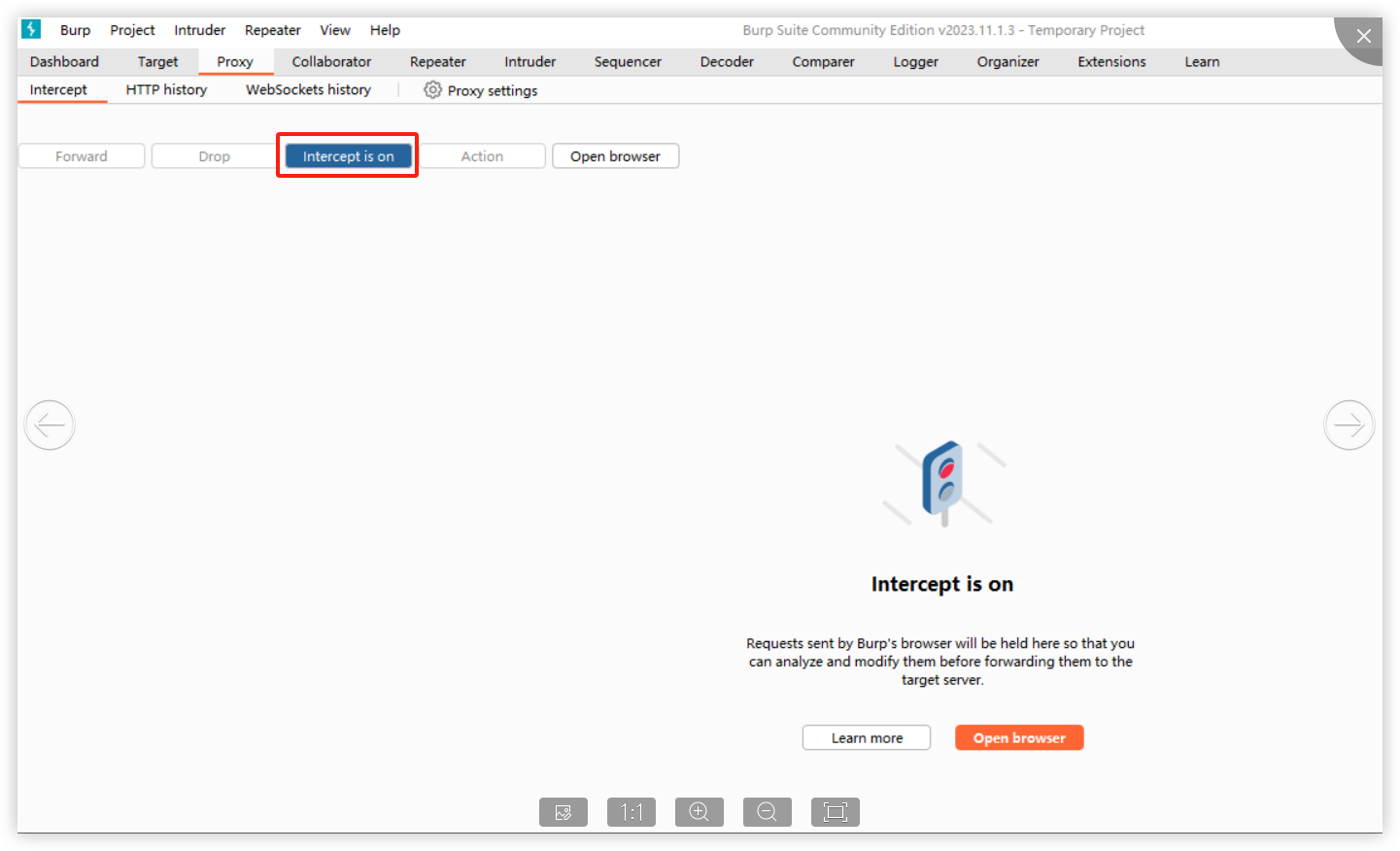 When opening the browser and entering the URL (allowing the first intercepted packet through Burp), the following is displayed: 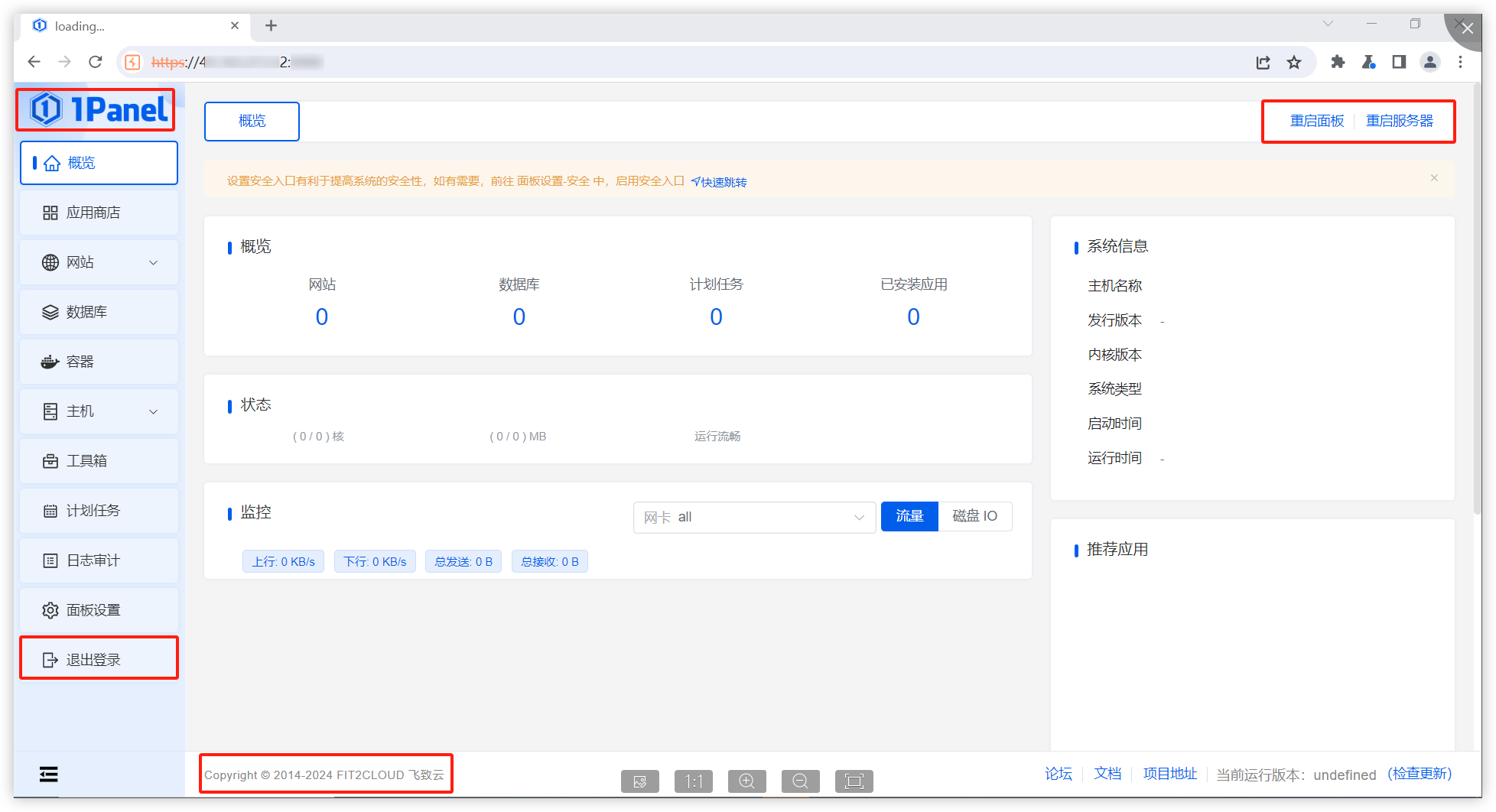 It is found that in this situation, we can access the console page (although no data is returned and no modification operations can be performed)." Affected versions: <= 1.10.0-lts ### Patches The vulnerability has been fixed in v1.10.1-lts. ### Workarounds It is recommended to upgrade the version to 1.10.1-lts. ### References If you have any questions or comments about this advisory: Open an issue in https://github.com/1Panel-dev/1Panel Email us at wanghe@fit2cloud.com
Metadata
Created: 2024-03-06T15:29:11Z
Modified: 2025-02-11T19:03:36Z
Source: https://github.com/github/advisory-database/blob/main/advisories/github-reviewed/2024/03/GHSA-26w3-q4j8-4xjp/GHSA-26w3-q4j8-4xjp.json
CWE IDs: ["CWE-863"]
Alternative ID: GHSA-26w3-q4j8-4xjp
Finding: F006
Auto approve: 1
